- Upgrade your defenses, not your anxiety. Let’s Talk! Contact Us

Audio Video Forensics Analysis: How Experts Examine Recordings
Introduction:
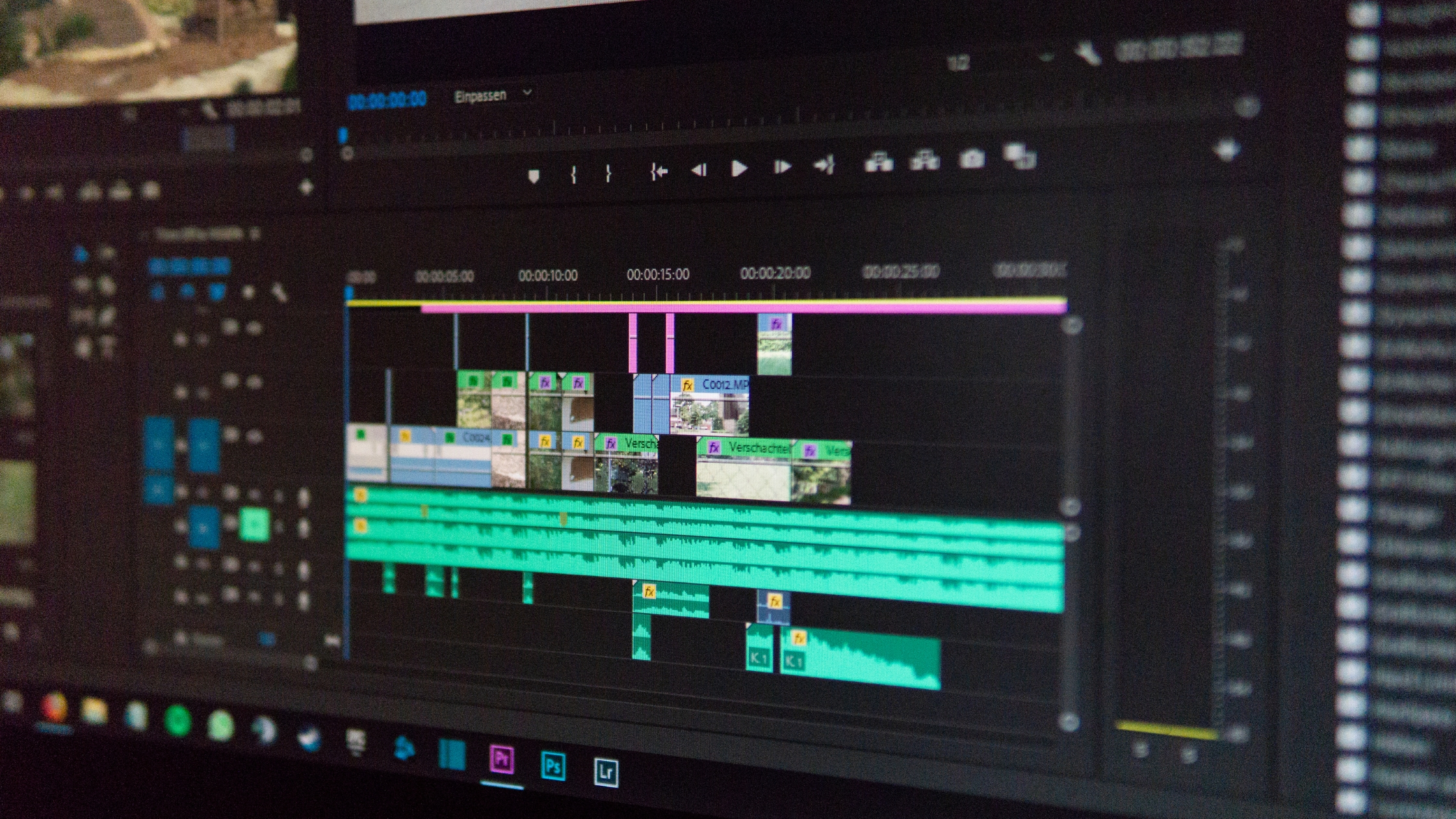
Audio and video recordings are a more common component of many industries today in the area of evidence, whether for law enforcement, corporate investigations, or personal disputes. Audio and video recordings can provide the required information to define facts, about events or conversations that may otherwise never be fully known. With the advancements of digital editing software in today’s environment, the challenge is that anything we hear, or see, on an audio or video audio recording could be suspectable to legibility. This opens the scope for audio-video analysis in the inquiry of audio-video digital forensic analysis.
Digital forensics consists of the methods to recover, analyse, and preserve data from digital devices to establish facts, while providing evidence, for inquiries. For audio and video evidence, forensic specialists use methods to verify, identify and authenticate a recording and verify whether the recording has been affected, compromised, or otherwise, manipulated. Authenticity for audio-video evidence, is important as it preserves the integrity of the evidence, and that it will be presented to the court, or any other relevant determination as legitimate evidence.
The process of audio video analysis involves verifying the authenticity, completeness, and editability of a sound or video recordings. Audio video analysis is an important component of digital forensics, which utilizes digital evidence to find the truth.
In its simplest form, audio video analysis, assesses whether alterations were made to any audio or video file. For example, someone may alter a conversation by removing conversation, changing a voice, or removing frames of a video file. Audio video analysis can detect those alterations for authenticity purposes.
Audio video analysis is typically used for:
Legal investigations, to support or oppose evidence in court.
Workplace issues or disputes to verify claims related to meetings or interviews.
Digital video footage and recorded conversations may contain key content that reveals what happened.
Public concern (online) or verification of viral videos, audio clips or films for issues related to fake or misleading content.
Audio video analysis helps provide, contextually, professional, legal and personal decisions-based sound and video evidence.
Why Audio and Video Evidence needs to be Verified:
Audio and video files are often used as important evidence when investigating a situation. These files can affect decisions being made in courtrooms, workplaces, insurance claims, and even public perception. But what if the evidence is not valid? What if audio is edited, taken out of context, or completely fake?
This is why audio and video verification are so important.
When the audio or video is used as evidence to prove what someone did or said, accuracy and authenticity are paramount. A single frame of video or a few seconds of audio can easily mislead people by creating another impression, even if completely accidental.
Here are some reasons why verification is critical for audio and video recordings:
Helps protect the truth: It will ensure that only verified information is being relied upon in any decision-making processes.
Prevents manipulations: It stops people from manipulating media by letting them twist facts or outright lie.
Provides fair outcomes: Verified evidence leads to fairer and more reliable results whether in a legal process, or corporate dispute.
There is a potential for serious consequences if fake or manipulated audio and video files are accepted as fact without any parsing. Audio video verification can minimize that risk by ensuring the evidence is accurate, valid, and reliable.
Key Things Experts Look for During Analysis
When forensics experts examine audio or video files, they systematically investigate any changes to the recording to determine if it is an original or altered recording. Although they employ advanced equipment, the purpose is quite simple: to determine if there are any indications that something may not be right.
Here are some of the main things they look for:
1. Unusual Cuts or Gaps
Experts check for parts of a video or audio file that seem to be missing or suddenly jump. These gaps can be a sign that the recording was edited to hide something. Any sudden transitions between segments may indicate a deliberate attempt to remove content or manipulate the timeline of the recording. The presence of these gaps often raises questions about the authenticity of the material.
2. Changes in Sound or Voice
They listen closely for differences in tone, background noise, or voice patterns. If someone’s voice changes suddenly, or if a sound doesn’t match the rest of the recording, it might mean the audio was changed or pieced together. Inconsistent audio quality or the unnatural alteration of voices may suggest the recording has been tampered with, and the expert will analyse the sound to verify its continuity and authenticity.
3. Video Frame Problems
A video is made up of many still images called frames, and several frames are shown every second. If some of these frames are missing or out of order, it may show the video was trimmed or altered. Experts will also look for signs of video “stitching,” where clips have been artificially combined, causing noticeable jumps or disruptions in motion. Frame analysis helps reveal whether the video was cut, reordered, or artificially inserted.
4. Inconsistent Backgrounds or Lighting
If the lighting, shadows, or background noise changes too quickly, it could mean that parts of the recording were added from a different time or place. This might include differences in the quality of lighting or slight shifts in the environment that don’t match the rest of the video. Such inconsistencies can point to editing or the insertion of new elements into the recording, compromising its authenticity.
5. File Information (Metadata)
Every digital recording comes with hidden information—like when and where it was made. Audio forensic experts check this data to confirm if the file is really from the time and device it claims to be. Metadata analysis can also reveal if the file was modified after its initial creation, which is crucial for validating the authenticity of the recording. In some cases, the metadata might be altered to conceal edits, so forensic experts examine this closely for any inconsistencies.
The verifications help demonstrate that nothing has been altered, added to, or removed from the original recording. When audio video analysis is done right the answers are clear and it is easy for people to have confidence in what they are seeing and hearing.
Process of Audio Video Analysis:
Audio Video Analysis in digital forensics is generally structured in a manner that provides for thorough, accurate, and professional analysis of the evidence. While the mechanics that are involved can be technical, here is a simple and more involved description of what typically happens:
1. Receiving the Original File
The process begins with collecting the original version of the audio or video file. This is important because copies or compressed versions can lose quality or contain added noise. The original file holds the most accurate data, which helps experts detect any signs of editing or tampering. If the original isn’t available, the highest-quality version is used.
2. Securing and Preserving the Evidence
Once the file is received, it is stored in a secure environment to prevent any changes, intentional or accidental. Experts maintain a detailed record of how the evidence is handled, including who accessed it and when. This is called a chain of custody, and it ensures that the evidence can be trusted in legal or official proceedings.
3. Step-by-Step Examination
The forensic team closely inspects the audio or video. For video, this might include checking each frame, studying movements, lighting, and sound consistency. For audio, experts listen for any unusual gaps, changes in tone, or background noise that doesn’t match the rest of the file. They may use specialized software to slow down the footage, isolate sounds, or zoom into specific visual elements.
4. Comparing with Other Information
In many cases, the analysis involves comparing the recording with other sources. For example:
Matching a voice with a known speaker.
Checking timestamps against call logs or security camera schedules.
Comparing video footage with still images or public data to confirm location and time.
These comparisons help confirm whether the audio or video fits the claimed context, such as a specific date, place, or person.
5. Creating a Clear, Court-Ready Report
After the analysis is complete, the expert prepares a written report that explains their findings. The report covers:
Whether the recording was altered or remains intact.
What signs of tampering (if any) were found.
A summary of the methods used to reach these conclusions.
This report is written plainly and without technical terminology so that lawyers, investigators, company executives, or even perhaps a judge will comprehend the results. The expert, if needed, could testify in court to explain their findings in person.
The stakes in reviewing sensitive audio/video evidence are exceptionally high. Whether it's a criminal case, corporate dispute, or personal situation, there is a heavy weight placed on integrity in all digital evidence. Unfortunately, not all forensic labs can manage sensitive audio/video evidence with the precision, care, and professionalism it demands at this level. When you trust a certified forensic lab such as Proaxis Solutions, you can be certain your evidence is cared for with the highest level of accuracy, transparency, and trust. In cases or situations where the truth matters, arrive at the foundation of truth with Proaxis Solutions, be a trusted partner.
Here’s why working with an expert forensic team like ours is essential for the success of your case:
1. Proven Accuracy and Reliability
At Proaxis Solutions we recognize that any digital evidence can only be examined to the degree of precision and consistency that is expected. Therefore, we utilize forensically sound, scientifically validated court-approved methods that have been tested and accepted by the legal and law enforcement community.
Our audio video forensic experts adhere to the accepted standards, and they will examine every one of your audio/video recordings for signs of manipulation, tampering or inconsistencies. We employ significantly advanced algorithms and provide various forensic techniques, such as digital fingerprints, waveform analysis, metadata analysis and frame-by-frame analysis. Using these methods, we are able to find the tiniest of changes that will demonstrate the results we provide are not only accurate but reliable.
It does not matter whether your matter is a highly investigated legal dispute, workplace investigation or any other critical situation; you need findings that you can stand behind. The findings are based on methods that are, and we will stand behind our findings at any professional level.
2. Confidential and Secure Handling
Digital evidence can be very sensitive material, particularly with respect to any personal privacy interests, protection of corporate secrets, or legal issues involved. Proaxis Solutions will take every reasonable precaution regarding confidentiality and security throughout the forensics process.
When your evidence is received and during the analysis and reporting stages, we adhere to strict protocols to protect and preserve your evidence from unauthorized or unintended access, tampering, or destruction. The data protocols we use to secure and preserve every piece of evidence include state-of-the-art encryption and a high level of security for file transfers and share with only those personnel designated with restricted access in the authorized access logs.
To track every action taken with your evidence we have implemented and follow chain of custody procedures. The protocols track who accessed or handled the evidence file and document every stage of the forensics process so there will always be a clear and trustworthy record to refer to establish traceability for the evidence. If your case proceeds to litigation or court, you can feel confident presenting your evidence without suspicion of its authenticity.
3. Clear, Court-Ready Reporting
One of our strongest attributes is our ability to present forensic findings in a concise, thorough, and understandable format. We recognize that prosecutors, or within corporate boardroom settings, or in personal consultations, often require that forensic findings be delivered without excessive technical jargon. Our expert team produces court-ready reports written in plain language that can be understood by legal professionals, investigators and corporate leaders as well as judges or juries.
Our reports are designed to present findings in a manner that makes it clear, so that any reader (regardless of any digital forensic background) can clearly understand the relevance of the analysis. Reports identify:
If the recording was altered or was original.
What alterations or lack of credibly was found (if any).
How we confirmed the authenticity of the recording.
Any recommendations or conclusions with respect to the findings.
This specificity of presentation has helps you to present findings without hesitation in court, at judgement hearings, and internal investigations.
4. Advanced Technology and Skilled Experts
At our lab, we don't solely rely on outdated equipment or basic techniques. We leverage the latest forensic technology available to us to ensure that each analysis and report is as accurate and thorough as possible, including the highest-quality software for audio analysis, video frame analysis, voice verification, and metadata analysis, along with many additional forensic tools.
However, technology alone is limited in its impact. What makes this all possible is the skilled forensic experts with experience and knowledge. Our team has undergone extensive training and experiences in the forensic field, working on a wide range of cases, including criminal matters, corporate fraud, personal disputes, and more. They are experienced at interpreting difficult pieces of digital evidence and know the appropriate techniques to use to account for subtle forms of manipulation.
It is the combination of state-of-the-art forensic tools and highly trained forensic experts that ensures thorough review of your audio or video evidence to maintain accuracy, reliability, and truthfulness.
5. Recognized by Legal and Professional Communities
Our reputation for reliability, accuracy, and timeliness in forensic analysis has made Proaxis Solutions a name widely accepted in the legal, law enforcement and corporate arenas.
Our work has played an essential part in a number of legal cases, corporate investigations and civil disputes, providing forensic results that have always been accurate and stood up in court. We have cultivated long-term working relationships with lawyers, insurance companies, attorneys, and investigators, and corporate personnel, all of whom acknowledge and trust our forensic services because of our accuracy and professionalism.
We also strive to assure that we are constantly learning, tools are latest, and techniques are latest in digital forensics. By staying up with the latest technologies and methodologies, we continue to provide forensic services in the forefront of the industry. This level of commitment to staying on top of industry shifts provides highly reliable and accurate service to you, ensuring you can feel completely confident that Proaxis Solutions is fully equipped to handle any level of complex and challenging digital events and scenarios, successfully, accurately, and with a high level of digital expertise.
Conclusion:
In a world of digital media that can be changed, distorted, or misinterpreted, verifying audio or video is crucial in helping digital forensics determine what the truth is. When you have a potential lawsuit or other workplace issue, trying to assess a potential impact on you or your business reputation resulting from a public allegation, you can insure against a blunder that could weaken your case or position by verifying the recordings.
Audio and video evidence should never be taken at face value. With solid forensic work, hidden edits, unverifiable claims, and digital manipulation can be discovered, leading lawyers, investigators, companies, and individuals to make informed decisions based on real, work product.
Our sole purpose at Proaxis Solutions is to provide transparent, honest, and professional forensic services that will hold up to challenge. We can help you figure out the truth (one recording at a time) - whether you need audio authentication, video authentication, or video verification.
If you have a recording, you need verified or analysed, don’t leave it to guesswork. Contact Proaxis Solutions for trusted forensic support.
Email: info@proaxissolutions.com
FAQs:
1. What is Audio and Video Forensic Analysis?
Answer:
Audio and video forensic analysis is the process of verifying the authenticity and integrity of audio and video recordings. This involves identifying any alterations, manipulations, or edits that may have occurred in the media. Forensic experts use specialized techniques to detect inconsistencies in sound, video frames, metadata, or other technical aspects, ensuring that the evidence is legitimate and unaltered.
2. Why is Audio and Video Evidence Verification Important?
Answer:
Audio and video recordings are frequently used as critical evidence in legal, corporate, and personal disputes. Verifying their authenticity ensures that the evidence can be trusted in decision-making processes. Unverified media can lead to false conclusions or manipulations that affect court rulings, workplace disputes, insurance claims, and public perception. Proper verification prevents fraud, manipulation, and misinterpretation of evidence.
3. What Are the Common Signs That an Audio or Video Recording Has Been Altered?
Answer:
Experts typically look for several signs when analysing audio or video recordings:
Unusual Cuts or Gaps: Missing segments or sudden jumps in the media.
Changes in Sound or Voice: Inconsistent tone, background noise, or voice alterations.
Frame Issues in Video: Missing or out-of-sequence frames that suggest editing.
Inconsistent Backgrounds: Changes in lighting, shadows, or environmental sounds that indicate manipulation.
Metadata Discrepancies: Irregularities in timestamps or file details.
4. How Do Forensic Experts Analyse Audio and Video Evidence?
Answer:
The forensic analysis process involves several stages:
Receiving and Securing Evidence: Collecting the original file and ensuring it is stored securely to prevent tampering.
Examination: For audio, experts listen for unusual sounds, gaps, or voice discrepancies. For video, they analyse frames, movement, lighting, and timestamps.
Comparative Analysis: Experts may compare the recording with other evidence like phone logs, security footage, or known samples to verify its context.
Report Preparation: A clear, detailed report is prepared to summarize the findings, including any alterations or tampering detected.
5. What Are the Tools and Software Used for Audio and Video Forensic Analysis?
Answer:
Audio and video forensic experts use specialized software and tools, including:
Audio Analysis Tools: To detect manipulation in sound recordings, isolate voices, or identify background noise anomalies.
Video Forensic Software: To analyse video frames, detect frame manipulation, and verify timestamp consistency.
Metadata Analysis Tools: To examine hidden data embedded in the file, such as creation date, device information, and edits.
Voice Recognition Systems: To compare voices and confirm the identity of speakers.
These tools are combined with expert knowledge to ensure the analysis is thorough and accurate.
6. How Long Does an Audio or Video Forensic Analysis Take?
Answer:
The time required for forensic analysis depends on the complexity and length of the recording, as well as the specific requirements of the case. On average, a thorough analysis can take anywhere from a few days to a couple of weeks. If the recording is part of a high-stakes legal case or urgent corporate investigation, expedited services can often be arranged.
7. Can Audio and Video Forensic Analysis Be Used in Court?
Answer:
Yes, audio and video forensic analysis results can be used in court. Forensic experts provide clear, concise, and court-ready reports that explain their findings. If necessary, they can testify as expert witnesses to support the validity of their analysis. It is essential that the forensic analysis meets accepted standards to ensure its reliability in legal proceedings.
8. What is Chain of Custody and Why is It Important?
Answer:
Chain of custody refers to the documentation process that tracks the handling of evidence from the moment it is collected to when it is presented in court. Ensuring a proper chain of custody is crucial to maintain the integrity of the evidence. Any break in the chain can cast doubt on the authenticity of the recording and potentially render it inadmissible in court.
9. Can You Detect If a Video Has Been Deep-faked?
Answer:
Yes, forensic experts can detect deepfake videos by analysing inconsistencies in the video’s visual and audio elements. These may include unnatural facial movements, discrepancies in lighting and shadows, or audio mismatches. Advanced forensic techniques such as facial recognition, frame-by-frame analysis, and digital fingerprinting are used to identify manipulated content.
10. What Should I Do If I Suspect an Audio or Video Recording Has Been Altered?
Answer:
If you suspect that a recording has been altered, it’s important to have it analysed by a certified forensic expert as soon as possible. Do not make any changes to the file, as this could compromise its integrity. Reach out to a trusted forensic lab, like Proaxis Solutions, to ensure that the evidence is properly analysed and preserved for further action.
11. How Do You Ensure Confidentiality When Handling Sensitive Audio or Video Evidence?
Answer:
At Proaxis Solutions, we adhere to strict confidentiality protocols. All evidence is stored securely, and access is strictly controlled. We document every action taken with the evidence to ensure a transparent chain of custody. Our forensic analysts and staff are trained to handle sensitive information with the utmost care and professionalism, ensuring that your case remains private and secure.
12. How Much Does Audio and Video Forensic Analysis Cost?
Answer:
The cost of forensic analysis depends on various factors, such as the length of the recording, the complexity of the analysis, and the urgency of the case. We offer customized quotes based on the specific needs of your case. For a more accurate estimate, please contact us to discuss the details of your recording and analysis requirements.
13. How Can I Submit My Audio or Video File for Forensic Analysis?
Answer:
To submit your audio or video file for forensic analysis, simply send a email to – info@proaxissolutions.com and We will guide you through the process, including how to securely upload your file. We ensure that your evidence is handled with the highest level of security and professionalism.
14. What Types of Cases Can Audio and Video Forensic Analysis Be Used For?
Answer:
Audio and video forensic analysis can be used in a variety of cases, including:
Legal Investigations: Verifying evidence presented in court, such as surveillance footage or recorded conversations.
Corporate Investigations: Analysing meeting recordings, interviews, or internal communications in workplace disputes.
Criminal Cases: Verifying video evidence from security cameras or audio recordings from wiretaps or emergency calls.
Personal Cases: Authenticating personal recordings, such as family videos or social media content, in disputes or allegations.
15. Why Should I Choose Proaxis Solutions for Audio and Video Forensic Analysis?
Answer:
Proaxis Solutions offers reliable, court-approved audio video forensic services. We use advanced tools, follow internationally recognized standards, and provide clear, easily understandable reports. Our team is skilled at identifying hidden edits and manipulations in audio and video recordings, ensuring that you get accurate, trustworthy results. Whether for legal, corporate, or personal matters, you can rely on us for confidential, professional, and precise forensic services.
Search
Popular categories
Forensics
32Cybersecurity
23Case Studies
1Latest blogs

How Insider Data Theft Happens & How to Investigate It
/Digital+Forensics+Services-+Proaxis+Solutions.webp)
Digital Forensics vs Incident Response (DF vs IR): Key Differences, Use Cases & When You Need Each

Write a public review